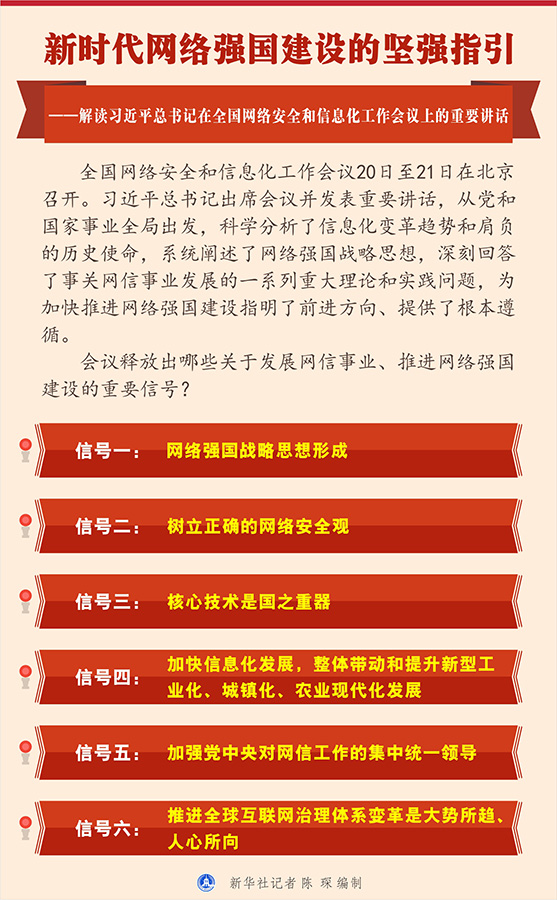
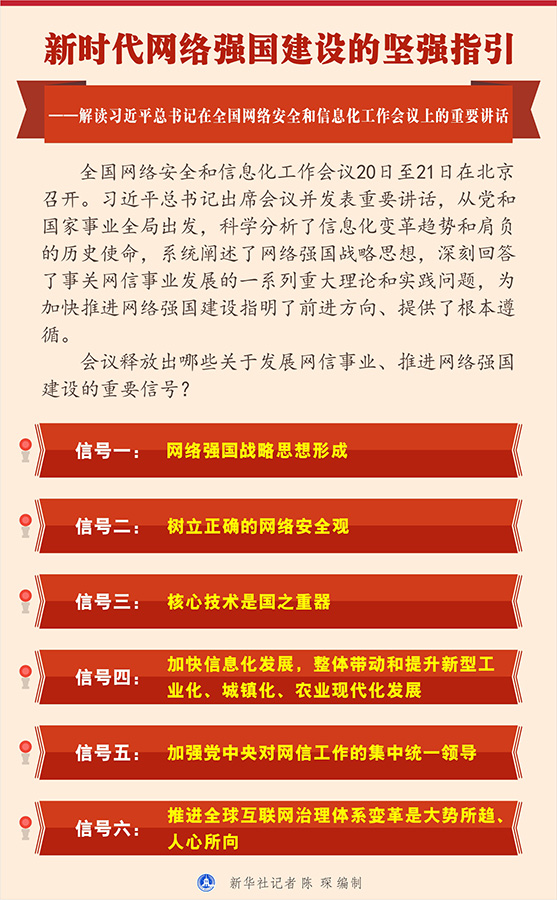
Chinese Military Focus on Cognitive Domain Warfare is the New Focus of Main Effort for Battlefield Confrontation

來源:人民網
認知域作戰是指運用輿論、心理、法律等多域手段,運用現代網絡、媒體、文字、圖片、視頻、數字等多維技術開展輿論宣傳。 、心理攻防,以及爭奪人心、顛覆信心、影響信仰、爭奪思想、意識形態鬥爭等重要形式,旨在爭奪人們在思想、信仰、價值觀、個人態度、情感、認同、 和判斷傾向。 認知領域戰是傳統輿論戰、心理戰、法律戰、貿易戰、外交戰、科技戰、意識形態戰等多領域戰的複雜集合。
目前,認知域作戰已經成為國家間軍事鬥爭和其他領域鬥爭的重要基礎,認知域目標驅動的語言對抗成為認知域作戰的重要形式,值得高度重視。 .
影響作戰對象的語言對策新前沿
認知領域作戰是當代認知科學研究和發展的伴隨成果。 它是人們積極探索大腦的認知活動,以期對大腦有更複雜、更抽象、更透徹的認識而產生的新戰場。 高級深度隱蔽活動是對行動對象影響的高端形式。 無論是信息行動的對象、信息的生產者、信息的內容本身,還是信息的傳播渠道,認知域中的操作都貫穿著認知的特徵,從一開始就突出認知層面的行動 結束。
從信息接收者的角度來看,這種認知是針對對手受眾的深度認知,包括其人民、軍隊、軍方指揮官或重要領導人、政商界重要人物,甚至直接包括 對方國家或軍隊的領導人。 具體的重要將領等,也可以是具體的人群或人群。 它可以涉及個人或群體的認知偏好、認知缺陷、認知習慣、認知偏見、認知誤解; 它還可以是個人和群體的信仰、價值觀、政治認同、族裔認同、社會和文化認同以及情感態度。
從信息提供者和內容的角度來看,應該融入信息生產者的認知設計和安排,包括對文本的獨特認知,如文本的話語方式、文本的敘述方式、 觀察事物的視角、敘述的認知重點和深度、句子的組織形式、句子的價值觀念傾向、句子概念的可接受性等。
在信息發布和傳播的渠道上,文本形式更接近多媒體多模態形式,更接近網絡空間的需要,更接近當代智能手機的優勢,更接近當前新興媒體時代的特徵,即 是,更符合受眾接受的認知特徵,即認知習慣和認知傾向。 文本的傳播形式充分考慮了國際傳播中的認知效應,尤其是跨文化、跨語言、跨媒體、跨群體的認知傳播。 這樣,文本會更好地從認知層面影響受眾。
語言對抗應對戰鬥風格的變化並產生新的戰術
縱觀人類歷史,不難發現,軍事鬥爭的風格一直在不斷變化。 從最初借助冷兵器的肉搏戰,發展到機械力與熱兵器的較量,也發展到高科技戰爭條件下信息能力的製衡。 每一次變化都帶來戰術上的深刻變化。 在當前機械化、信息化、智能化並存的過渡階段,人們不僅關注戰場物理域和信息域的主導權爭奪,更關注對戰場主體的控制。 戰爭-人類認知領域,即思維方式、認知模式和風格、價值觀、情感態度、文化模式、溝通模式、心理優勢和劣勢、認知偏好、文化和知識圖譜以及意識形態認同。 後者涉及基本情況
對社會人事和社會存在的影響,即認知領域運作的新興領域,其策略具有很強的特殊性。
話題靈活性和機動性:認知域作戰可以在認知域中選擇多個話題進行靈活機動的作戰行動。 根據現狀和需要,選題可以選擇涉及比較宏觀的戰略層面(比如對方整個社會的意識形態和製度等),或者中等層面的運動層面(比如社會問題) 在對方社會的局部或方向:社會福利政策或環保政策等),也可以選擇涉及社會中非常微觀的戰術問題(比如社會不公平、不公正、不美好的一面) 由某個人或特定事件反映)。 宏觀、中觀和微觀認知領域相互聯繫、相互轉化。 很可能一個微觀問題也會成為一個宏觀的戰略問題。 要根據與整個軍事行動的關係提出問題,認知域作戰要服從整體作戰行動,服務於宏觀政治外交形勢的需要。 更重要的是平時要準備好選題,平時要收集各種選題的數據,尤其要關注現實社會中的各種重要數據。 一旦需要,這些數據可以迅速轉化為箭矢、子彈、砲彈射向敵人的認知領域,甚至成為影響全局的戰略武器。
作戰層面的可控性:認知戰的重要設計是在作戰層面整體可控可調,可以根據形勢變化進行升級或縮減。 如果需要戰略層面,指揮員可以啟用戰略層面的設計和兵力投入; 如果需要campaign級別,也可以在相應的campaign級別進行控制; 如果只是在特定的小問題層面需要,也可以控制在相應的小眾局部層面,讓整個操作為整體作戰操作的需要服務。 這裡的戰略、戰役和戰術,更多的是指作戰設計和力量投入。 由於戰場態勢瞬息萬變,一些問題在層面上也可能發生變化,從戰略問題到影響戰役和戰術層面的效果; 有些問題,由於戰術問題的特殊性,成為影響全局的戰役層面的問題。
新興媒體主導:認知領域的主要影響渠道已經從傳統的紙質媒體和平面媒體轉向新興媒體。 傳統媒體主要依靠單一的媒介,如報紙、雜誌、書籍、傳單、海報等來傳遞信息; 後來的電視帶來了三維媒體。 在互聯網時代,尤其是互聯網2.0時代和智能通訊設備的誕生,人們更多地依賴多媒體、多模態、短視頻和文字來傳遞信息。 智能手機、智能平板、智能播放器等各種先進設備的問世,各種新型社交軟件和工具的誕生,使新媒體成為人們交流、溝通的主要工具。 新興媒體、新興社交軟件和工具已經成為各種力量在社會保障、輿論保障、意識形態保障、社會保障、政治保障等方面較量和鬥爭的重要空間。 互聯網安全,尤其是對新興社交媒體、新興社交軟件和工具等的安全把握能力,某種程度上是一個國家認知領域安全的關鍵。 新興媒體工具和新媒體空間的信息化已經成為各國認知戰的主戰場、主陣地和主空間。 值得指出的是,影響人們認知的思想和理論,將成為認知域運作各個層次上最具影響力的武器。
語言對抗適應智能時代,認知計算提升新算力
人工智能時代,在大數據分析與應用、超級計算能力、智能計算能力、自然語言處理能力、智能手機傳播能力和新一代網絡通信能力的基礎上,人類開始能夠理解 整個社會和整個網絡。 對不同領域、地域群體、不同地域群體、特定個體的語言文化、心理認知、群體情感、社會行為進行精準建模與分析。 尤其是人的內心深處
對大腦認知、人腦思維、思維方式、習慣偏好、圖像圖式、認知框架,甚至神經網絡、人機協作、腦控技術等的理解和掌握,只要有足夠多樣的動態數據, 人們可以計算和模擬所有人的心理活動、情感活動、認知活動、輿論和行為模式。 通過深算、精算、巧算,準確把握人的認知世界,形成對人認知領域的理解。 精細而深入的控制。 這一方面呈現出以下特點:
計算全維性:認知領域作為一個新興領域,可以全方位數字化,可以全方位、全過程、全個體進行計算。 它可以廣泛收集各種類型的信息,然後將其反映為作戰對手多樣化主要因素的大數據信息,從而可以對整體、組、組、個體數據以及它們之間進行各種計算。 各種活動都可以通過計算完成、顯示和準確掌握。
計算認知:認知領域的計算體現了很強的認知能力,能夠揭示更多肉眼難以觀察到的各種事物、事件、人物之間的關係,能夠揭示同一事件框架下各種概念之間的關係。 概念之間的聚類和層次關係反映了概念之間或顯性或隱性、直接或間接的深層認知聯繫,揭示了概念之間複雜的概念網絡系統,讓人看到一個完全超越普通肉眼的深層認知世界 觀察。 .
計算智能:認知領域的計算體現了強智能。 這種智能表現在計算上,會得出智能的結論。 例如,通過大量文本的收集和數據挖掘,我們可以找到由於人力有限而無法看到的各種主題、觀點、傾向、人群、立場和訴求之間的關係,從而 對某個問題形成更全面的認識。 全面、深入、準確、系統的認識,做出科學優化的決策。 這種決策可能符合人類智能,也可能超過甚至遠遠超過人類智能。 利用好認知計算的力量,特別是結合本國和對手的數據,可以更好地做到早預防、早預警、早部署,可以做到最好、最好、最快、最準的打擊 和反擊。 也更能體現高效、有力、針對性的保障。 這裡的認知計算更多的是一個可能出現在不同人群、不同時間段、不同背景、整個網絡域或局部網絡域、特定特定網絡域內的宏觀-中觀或微觀層面的問題。 團體。 特別是對與對手對局時雙方可能呈現的主動和被動情況的分析和考察,以及認知域的攻防等。
發揮話語主體地位釋放話語權新應用
認知域作戰有一個非常重要的支撐,即主要依靠語言媒介發揮作用,主要通過語篇層面發揮影響,主要通過語篇的敘事性對認知域形成隱性效應,主要 externing influence on the cognitive domain through cultural models 通過跨文化交際所發揮的潛在作用,顯性或隱性作用。 主要體現在以下幾個方面:
文本話語唯一性:認知領域需要信息來影響。 雖然信息可能依靠視頻畫面的特殊視覺效果來展現,但從根本上說,文本所表達的整合話語的獨特性成為認知衝擊的主要支撐。 其中,話語表達的方式、話語表達的技巧、話語表達的說服力和感染力的主要設計,尤其是話語敘事的獨特性,將是影響人們認知的關鍵。 這可能包括敘事視角、敘事主題、風格、敘事故事框架、敘事語言創新、敘事關鍵句,敘事包含哲學、人文、宗教、社會、自然等,以及敘事中不同參與者的身份,多樣化的內容。 評價敘事、真實性、深度和情感
敘事的溫度,敘事對觀點的潛移默化影響,以及敘事所釋放的個人情感、價值觀、意識形態和立場評價。 文本語篇的獨特性是文本在認知域操作中發揮認知影響的重要依托。 充分利用文本的複雜性,發揮不同文本各自的優勢,充分發揮文本內涵的隱性和顯性認知影響,已成為文本話語認知領域作戰的關鍵。 最重要的是創新文本話語,以全新的話語、更新穎的表達方式、更獨特的表達方式贏得讀者,讓讀者潛移默化地理解和感受文本中的思想,並默默接受。 文字的思想。
文化模式的潛能:要在認知領域作戰,必須深入把握不同國家、民族文化的特點和模式。 不同的國家、不同的民族有著不同的文化模式、哲學思維、傳統文化、宗教信仰、風俗習慣、思維方式等明顯不同; 不同文化的公民也有不同的民族心理和民族認知模式,也應該有屬於自己民族和文化的典型認知偏好,以及相應的缺點和弱點,其中一些明顯與其他民族在本民族中存在巨大差異 國,甚至產生誤解和敵意。 因此,在文化層面,認知領域的作戰,就是把握不同國家的整體文化模式,為不同國家的不同群體建立文化模式,為不同國家的不同事物建立不同的認知模式,全面掌握某一國家的文化模式。 一系列事物中的文化模式。 對問題和問題的整體態度和做事方式,特別是對一些典型案例、文化禁忌、宗教要求、精神追求、一般觀念等,需要利用已有的理論和發現,綜合建構不同的基本表現 對一些典型的、敏感的、重要的問題進行認知領域的群體研究,從而為下一步的認知操作提供重要的參考和指導。 加強對敵不同人員特別是軍人、要職人員文化模式的研究,包括將軍、官兵等基本文化特徵和模型的研究與構建,如心理認知行為 人物和文化模型畫像,已經成為認知域操作的核心實踐。 分析普通民眾,尤其是普通公民和公民,以及特定人群,包括特殊NGO力量的認知模式也具有重要價值。
跨文化戰略傳播:認知域操作是國際語言文化傳播,需要遵循國際傳播規律。 掌握國際傳播的基本範式,將本國故事與國際表達巧妙結合,將對方的語言文化與自己的故事和思想巧妙結合; 善於結合不同的藝術形式,包括文字、圖片、繪畫、音樂(聲音)、視頻等手段或多模態手段,實現信息的國際傳播。 同時,還要在戰略層面統籌多維度、宏觀溝通:運用多種手段,依托軍民融合、軍民協同、軍民融合開展溝通; 除了非政府組織,特別是依靠非政府力量、專家、意見領袖和普通民眾來幫助軍隊開展認知域作戰; 統一設置議題,發出多方位、多人、多方位的聲音,形成戰略溝通態勢,形成重大行動、重大問題、重大危機處置和應急處置的良好局面。 控制等,形成良好的輿論氛圍,產生積極影響,消除不利影響或消除不利影響。 尤其要建立一支精通外語、通曉跨文化、通曉國際交流規律、能在國際多維平台上暢所欲言的精幹團隊。 這些人員通常可以藉助常見或特殊問題進行廣泛的問題認知、收集和討論,建立人脈和粉絲群; 更重要的是,在關鍵時刻,通過自己的粉絲團,發揮影響力,完成戰略傳播任務。

目前,隨著混合戰、多域戰和全球戰的普及,認知域戰已經成為一種常見的混戰方式。 、法律戰發展的高級階段、複雜階段和升級階段。 它的興起更具欺騙性、曖昧性、隱蔽性、嵌入性、植入性和不可觀察性,特別是考慮到它與當代新興媒體的深度融合,不斷學習和借鑒多學科、跨學科、交叉的新思想、新技術、新方法。 於是,認知領域的戰鬥成為我們必須高度警惕的戰斗形式。 (國防科技大學文理學院教授、博士生導師 梁曉波)
【本文為國家社科基金重大項目《國防和軍隊改革視角下的國防語言能力建設》的階段性成果】
Modern English Version:
Source:

Cognitive domain combat refers to the use of multi-domain means such as public opinion, psychology, and law, and the use of modern network, media, text, pictures, video, digital and other multi-dimensional technologies to carry out public opinion propaganda, psychological attack and defense, and The important forms of fighting for people’s hearts, subverting confidence, influencing beliefs, fighting for thinking, and ideological struggle are intended to compete for people’s initiative in thinking, beliefs, values, personal attitudes, emotions, identification, and judgmental tendencies. Cognitive domain warfare is a complex collection of multi-domain warfare such as traditional public opinion warfare, psychological warfare, legal warfare, trade war, diplomatic warfare, technological warfare, and ideological warfare.
At present, combat in the cognitive domain has become an important basis for military struggles and struggles in other fields between countries, and language confrontation driven by goals in the cognitive domain has become an important form of combat in the cognitive domain, which deserves great attention.
A New Frontier for Language Countermeasures to Influence on Objects of Operation
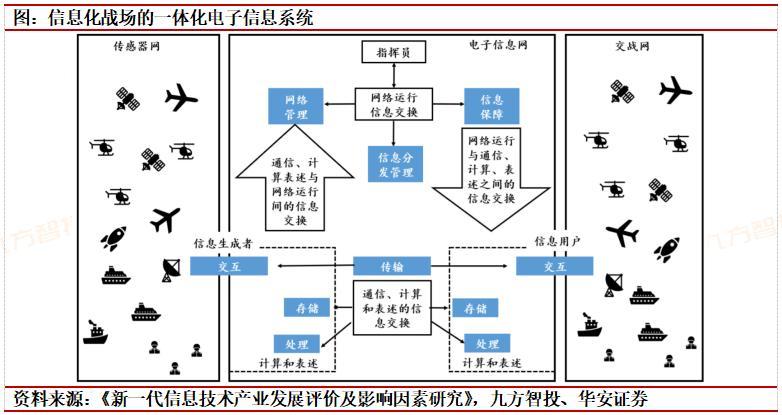
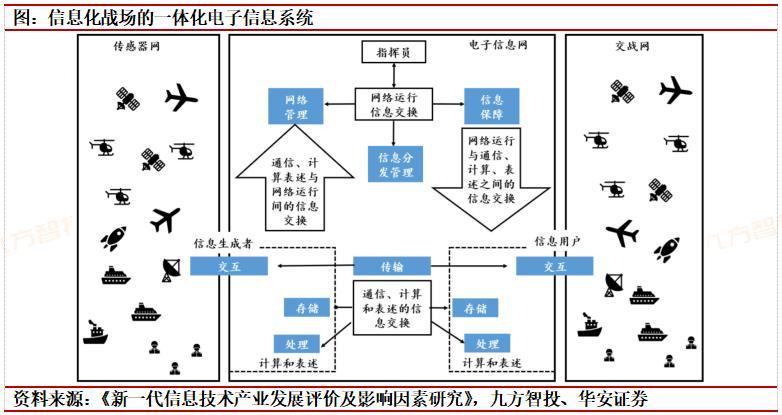
Cognitive domain combat is the accompanying result of the research and development of contemporary cognitive science. It is a new combat field created after people actively explore the cognitive activities of the brain to gain a more complex, abstract and thorough understanding of the brain. Advanced deep covert activities are the high-end form of influence on the object of action. Regardless of whether it is the object of information action, the producer of information, the content of information itself, or the channel of information, operations in the cognitive domain all run through the characteristics of cognition, and highlight actions from the cognitive level from beginning to end.
From the perspective of the recipients of the information, this cognition is aimed at the deep cognition of the opponent’s audience, including its people, the army, military commanders or important leaders, important figures in the political and business circles, and even directly including the leaders of the opponent’s country or the military. Specific important generals, etc., can also be specific groups of people or people. It can involve the cognitive preferences, cognitive shortcomings, cognitive habits, cognitive biases, cognitive misunderstandings of individuals or groups; it can also be the beliefs, values, political identity, ethnic identity, social and cultural identity and emotional attitudes of individuals and groups.
From the perspective of the information provider and content, it should be infused with the cognitive design and arrangement of the information producer, which includes the unique cognition of the text, such as the discourse mode of the text, the narrative mode of the text, the perspective of observation of things, the narrative Cognitive focus and depth, organizational form of sentences, tendencies such as value concepts of sentences, acceptability of concepts of sentences, etc.
In terms of channels for information distribution and dissemination, the form of text is closer to the multimedia multimodal form, closer to the needs of cyberspace, closer to the advantages of contemporary smartphones, and closer to the characteristics of the current emerging media era, that is, more in line with the audience The cognitive characteristics of acceptance are cognitive habits and cognitive tendencies. The form of dissemination of the text fully considers the cognitive effect in international communication, especially the cognitive communication across cultures, languages, media, and groups. In this way, the text will better influence the audience from the cognitive level.
Language confrontation responds to changes in combat styles and generates new tactics
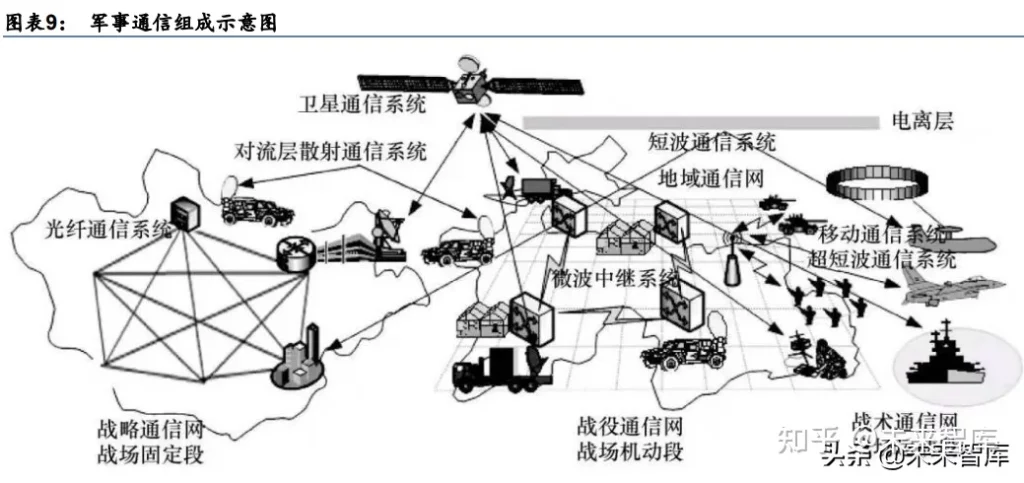
Throughout human history, it is not difficult to find that the style of military struggle has been constantly changing. From the initial physical fight with the help of cold weapons, it has developed into a contest of mechanical power with hot weapons, and has also developed into a check and balance of information capabilities under the conditions of high-tech warfare. Every change brings about profound changes in tactics. In the current transitional stage of co-existence of mechanization, informationization and intelligence, people not only pay attention to the struggle for dominance in the physical domain and information domain of the battlefield, but also pay more attention to the control of the main body of war-human cognitive domain, that is, the way of thinking, Cognitive models and styles, values, emotional attitudes, cultural models, communication models, psychological strengths and weaknesses, cognitive preferences, cultural and knowledge maps, and ideological identity. The latter involves the basic situation of social personnel and social existence, that is, the emerging field of cognitive domain operations exerting influence, and its tactics have strong particularities.
Topic flexibility and mobility: Cognitive domain operations can select many topics in the cognitive domain to carry out flexible and mobile combat operations. According to the current situation and needs, the topic can be chosen to involve a relatively macro strategic level (such as the ideology and system of the other party’s entire society, etc.), or a medium-level campaign level (such as social issues in a local area or direction of the other party’s society: Social welfare policies or environmental protection policies, etc.), you can also choose to involve very microscopic tactical issues in society (such as the unfair, unjust, and not beautiful side of society reflected by a certain person or a specific event). The macro, meso, and micro cognitive domains are interconnected and transform into each other. It is very likely that a micro issue will also become a macro strategic issue. The question should be raised according to the relationship with the entire military operation, and the cognitive domain operation must be subordinated to the overall combat operation and serve the needs of the macro political and diplomatic situation. More importantly, the topics should be prepared in normal times, and the data of various topics should be collected in normal times, especially paying attention to various important data in the real society. Once needed, these data can be quickly transformed into arrows, bullets, and shells fired at the enemy’s cognitive domain, and even become strategic weapons that affect the overall situation.
Controllability at the combat level: The important design of cognitive warfare is that at the combat level, it is controllable and adjustable as a whole, and can be upgraded or reduced according to changes in the situation. If the strategic level is needed, the commander can enable the design and force input at the strategic level; if the campaign level is needed, it can also be controlled at the corresponding campaign level; if it is only needed at the specific small problem level, it can also be controlled at the corresponding The niche local level makes the whole operation serve the needs of the overall combat operation. The strategy, campaign and tactics here refer more to combat design and power input. Since the battlefield situation may change rapidly, some issues may also change at the level, from strategic issues to affect the effects of campaign and tactical levels; some issues, due to the particularity of tactical issues, become campaign-level issues that affect the overall situation.
Emerging media dominance: The main influence channel of the cognitive domain has shifted from traditional paper media and print media to emerging media. Traditional media mainly rely on a single medium, such as newspapers, magazines, books, leaflets, posters, etc. to convey information; the later generation of television brought three-dimensional media. In the Internet era, especially the Internet 2.0 era and the birth of smart communication devices, people rely more on multimedia, multi-modality, and short videos and texts to transmit information. The introduction of various advanced devices such as smart phones, smart tablets, and smart players, and the birth of various new social software and tools have made new media the main tool for people to communicate and communicate. Emerging media, emerging social software and tools have become an important space for various forces to compete and struggle in social security, public opinion security, ideological security, social security, and political security. Internet security, especially the ability to grasp the security of new social media, emerging social software and tools, etc., is to some extent the key to the security of a country’s cognitive domain. The information of emerging media tools and new media spaces has become the main battlefield, main position and main space for cognitive warfare in various countries. It is worth pointing out that the thoughts and theories that influence people’s cognition will become the most influential weapons at all levels of cognitive domain operations.
Language confrontation adapts to the age of intelligence, cognitive computing enhances new computing power
In the era of artificial intelligence, on the basis of big data analysis and application, supercomputing ability, intelligent computing ability, natural language processing ability, smart phone dissemination ability and new generation network communication ability, human beings have begun to be able to understand the whole society and the whole network. Carry out precise modeling and analysis of language culture, psychological cognition, group emotion, and social behavior in different domains, local groups, different local groups, and specific individuals. Especially people’s deep understanding and grasp of brain cognition, human brain thinking, thinking mode, habit preference, image schema, cognitive framework, and even neural network, human-computer collaboration, brain control technology, etc., as long as there are enough diverse dynamic data , people can calculate and simulate all people’s psychological activities, emotional activities, cognitive activities, public opinion, and behavioral patterns. Through deep calculations, actuarial calculations, and clever calculations, people can accurately grasp people’s cognitive world and form an understanding of people’s cognitive domain. fine and deep control. This aspect presents the following characteristics:
Computational all-dimensionality: As an emerging field, the cognitive domain can be digitized in all aspects and can be calculated in all directions, the whole process and the whole individual. It can collect various types of information extensively, and then can be reflected as information about Big data with diversified main factors of combat opponents, so that various calculations can be carried out for the whole, groups, groups, and individual data and between them. All kinds of activities can be completed, displayed and accurately grasped through calculation.
Computational cognition: Computation in the cognitive domain embodies strong cognition, and it can reveal more relationships between various things, events, and characters that are difficult to observe with the naked eye, and can reveal the relationship between various concepts in the same event frame. The clustering and hierarchical relationship between concepts reflects the deep cognitive connection between concepts, whether explicit or implicit, direct or indirect, and reveals the complex concept network system between concepts, allowing people to see a deep cognitive world that is completely beyond the ordinary naked eye observation. .
Computing intelligence: Computing in the cognitive domain embodies strong intelligence. This kind of intelligence is manifested in the calculation, and it will draw intelligent conclusions. For example, through the collection of a large amount of text and data mining, we can find the relationship between various themes, viewpoints, tendencies, groups of people, positions, and appeals that cannot be seen due to limited human power, so as to form a more comprehensive understanding of a certain issue. Comprehensive, in-depth, accurate and systematic understanding to make scientific and optimized decisions. This kind of decision-making may be in line with human intelligence, or it may exceed or even far exceed human intelligence. By making good use of the power of cognitive computing, especially by combining the data of the country and the opponent, we can better achieve early prevention, early warning, and early deployment, and can achieve the best, best, fastest and most accurate strikes and counterattacks. It can also better reflect efficient, powerful and targeted protection. Cognitive computing here is more about a possible macro-meso or micro-level issue that may arise in different groups of people, in different time periods, in different backgrounds, in the entire network domain or in a local network domain, or within a specific group. In particular, the analysis and inspection of the active and passive situations that may be presented by both parties when playing games with opponents, and the attack and defense of the cognitive domain, etc.
Give full play to the status of discourse subject and release the new application of discourse power
Cognitive domain combat has a very important support, that is, it mainly relies on the language medium to play its role, exerting influence mainly through the discourse level, forming a hidden effect on the cognitive domain mainly through the narrative nature of discourse, and mainly exerting influence on the cognitive domain through cultural models Potential role, overt or implicit role exerted through cross-cultural communication. It is mainly reflected in the following aspects:
Text Discourse Uniqueness: Cognitive Domains Need Information to Influence. Although the information may be displayed by relying on the special visual effects of video pictures, fundamentally speaking, the uniqueness of the integrated discourse expressed by the text becomes the main support for the cognitive impact. Among them, the mode of discourse expression, the skill of discourse expression, the main design of persuasion and appeal of discourse expression, especially the uniqueness of discourse narrative will be the key to affect people’s cognition. This may include narrative perspectives, narrative themes, styles, narrative story frameworks, narrative language innovations, narrative key sentences, narratives contain philosophy, humanities, religion, society, nature, etc., and the identities of different participants in the narrative , the diversified evaluation of narrative, the authenticity, depth and emotional temperature of narrative, the subtle influence of narrative on viewpoints, and the personal emotions, values, ideology, and position evaluation released by narrative. The uniqueness of text discourse is an important reliance on cognitive influence exerted by text in cognitive domain operations. Making full use of the complexity of texts, giving full play to the respective advantages of diverse texts, and giving full play to the implicit and explicit cognitive influences of text connotations have become the key to combat in the cognitive domain of text discourse. The most important thing is to innovate text discourse, to win readers with brand-new discourse, more novel expressions, and more unique expressions, so that readers can understand and feel the thoughts in the text subtly, and accept them silently. The thought of the text.
Potential of cultural models: To fight in the cognitive domain, we must deeply grasp the characteristics and models of different countries and national cultures. Different countries and different nationalities have different cultural models, philosophical thinking, traditional culture, religious beliefs, customs, and ways of thinking are obviously different; citizens of different cultures also have different national psychology and national cognition Models should also have typical cognitive preferences belonging to their own nation and culture, as well as corresponding shortcomings and weaknesses, and some of them obviously have a huge difference from other nationalities in their own country, and even have misunderstandings and hostility. Therefore, at the cultural level, combat in the cognitive domain is to grasp the overall cultural models of different countries, build cultural models for different groups in different countries, build different cognitive models for different things in different countries, and fully grasp a certain country’s cultural models in a series of things. The overall attitude and way of doing things on issues and issues, especially for some typical cases, cultural taboos, religious requirements, spiritual pursuits, general concepts, etc. It is necessary to use existing theories and findings to comprehensively construct the basic performance of different groups of people in the cognitive field on some typical, sensitive, and important issues, so as to provide important reference and guidance for the next step of cognitive operations. Strengthen the research on the cultural patterns of different personnel of the enemy, especially military personnel, personnel in key positions, including the research and construction of basic cultural characteristics and models of generals, officers, soldiers, etc., such as the psychological cognitive behavior of characters and cultural model portraits, It has become the core practice of cognitive domain operations. It is also of great value to analyze the cognitive patterns of ordinary people, especially ordinary citizens and citizens, as well as specific groups of people, including special NGO forces.
Cross-cultural strategic communication: Cognitive domain operations are international language and cultural communication, which need to follow the laws of international communication. To grasp the basic paradigm of international communication, to skillfully combine national stories with international expressions, to skillfully combine the other party’s language and culture with their own stories and ideas; to be good at combining different art forms, including words, pictures, paintings, music (Sound), video and other means or multi-modal means to achieve the international dissemination of information. At the same time, it is also necessary to coordinate multi-dimensional and macroscopic communication at the strategic level: use various means, rely on military-civilian integration, military-civilian coordination, and military-civilian integration to carry out communication; in addition to non-governmental organizations, especially rely on non-governmental forces, experts, opinion leaders, and ordinary people To help the military carry out cognitive domain operations; to set up issues in a unified way, to make multi-point, multi-person and multi-dimensional voices, to form a strategic communication situation, to form a good situation for emergency solutions for major actions, major issues, major crisis management and control, etc., to form a good atmosphere of public opinion, and to create Positive effects, eliminating adverse effects or extinguishing adverse effects. In particular, it is necessary to establish a capable team that is proficient in foreign languages, understands cross-cultural skills, understands the laws of international communication, and can skillfully speak out on international multi-dimensional platforms. These personnel can usually carry out extensive issue awareness, collection and discussion, establish personal connections and fan groups with the help of common or special issues; more importantly, at critical moments, through their fan groups, exert influence and complete strategic communication tasks .

At present, with the popularity of hybrid warfare, multi-domain warfare and global warfare, cognitive domain warfare has become a common method of hybridization and mixing. , The advanced stage of the development of legal warfare, the complex stage and the escalation stage. Its rise is more deceptive, ambiguous, concealed, embedded, implanted and unobservable, especially considering its deep integration with contemporary emerging media, and continuous learning and reference into multidisciplinary, Interdisciplinary and interdisciplinary new ideas, new technologies, and new methods. As a result, combat in the cognitive domain has become a form of combat that we must be highly vigilant against. (Liang Xiaobo, professor and doctoral supervisor of the College of Arts and Sciences, National University of Defense Technology)
[This article is a phased achievement of the National Social Science Fund’s major project “National Defense Language Capacity Building from the Perspective of National Defense and Military Reform”]
Original Chinese Military Source: http://military.people.com.cn/BIG5/n1/2022/0517/c1011-32423539.html