China Military Theater System Reform Era of Information Warfare
中國軍事戰區制改革信息化戰爭時代中國軍隊應對新安全形勢的重大保障
習近平中國軍事改革
February 1, the PLA theater inaugural meeting held in Beijing. CPC Central Committee General Secretary and State President and CMC Chairman Xi Jinping granted flag to the theater and five issued a bull. Theater set up joint operations command structure, the CPC Central Committee and the Central Military Commission in accordance with domestic major strategic decision, made by the international situation changes, China will further promote the reform process in military forces, and greatly enhance the combat capability of the PLA.
Substantive reform: the military establishment system to adapt to new forms of information warfare needs
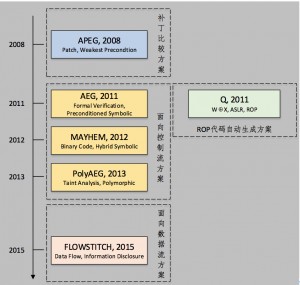
Military technology, military and military establishment system are the three basic elements of the new military revolution. Mankind has experienced a long weapon cold and hot steel age after the war and military technical thinking in the era of rapid development of mechanized warfare. The late 1970s, the Soviet Chief of Staff, Marshal of the Soviet Ogarkov Given the rapid development of military technology, forward-looking put forward the idea of military technological revolution, which started a new military revolution sweeping the globe; 1997 , the US military put forward the “network-centric warfare” concepts, theories began to appear new military revolution prototype – each a full revolution in military affairs, the military establishment were to promote institutional change by a large development of military technology and weaponry – it by military personnel and weaponry so that the army can be effectively combined to form an overall combat power key.
In 1998, China put forward the “information warfare” concept, explicitly stated that mankind is the fourth military revolution of information technology revolution in military affairs, marking the technical form of human warfare into the information age warfare from mechanized war era. Against this background, the PLA is to follow the above rules, after weapons and equipment technology has made rapid progress, the military regime began vigorously to prepare a series of reforms: December 31, 2015, the armed services mechanism reform is completed, set up a new army, rocket forces, strategic support of three services – army, navy and air force combined with the previous, form a pattern of five armed services; January 11, 2016, to complete the formation of organs of the Central military Commission departments, from the previous four general headquarters, JMC became 15 functional departments; February 1, 2016, five theater adjustment is completed, the previous seven military regions, adjusted to five theater.
The main reason: “military” system become shackles China Military Revolution and the development of military

Original seven military system schematic
From the founding of the early century, by the comprehensive national strength and defense spending restrictions, military equipment levels remained low, failed to achieve the goal of complete mechanization construction; and, when low domestic railway, highway construction level, under difficult conditions in a nuclear war support large formation in the territory of strategic mobility. By the above two limitations, only the army at the time of partition of defense, so that each major military all have independent ability to respond to a threat of strategic direction.
Nearly 15 years, accumulated through investment in national defense and army reform, China’s transport network has been done, “accessible”, the level of military equipment have been greatly improved – Preliminary mechanization and mobility of fighting units sharply higher, with the from “area defensive shift basis “to” trans-regional mobility. “After greatly improved mobility, combat troops in wartime may implement in different zones under the command of, and therefore no longer need to implement the military management by a specific military.
Also, in the “military” system, military and navy and air force the same level, but also under the jurisdiction of the military air force, and even the fleet, in fact, is the embodiment of “Continental Army” thought, there are some drawbacks: military orders, regardless of military inefficient. This system has become the shackles of China Military Revolution and the development of the armed forces, can not effectively respond to security threats or China is likely to face.
Perimeter security situation and the international situation changes, “theater” made a timely decision.
Theater, from a geographic dimension in terms of a multi-dimensional space, including a broad front, greater depth and possible operational target, it is mainly based on strategic and operational tasks delineated strategic and operational activities of the regional corps with the leadership and command bodies, forces have on the area command, the command level is between the high command and strategic battle between the Legion.The main basis for division of the theater, including changes in the international pattern of perimeter security situation, military strategy, political, economic, military status and geographical characteristics of the country, and many other aspects.
Since the reform and opening up, China’s economic construction has made remarkable achievements in comprehensive national strength rising rapidly driven by changes in national strategy occurred; the Soviet Union, China land border security threat disappeared, and security threats from maritime direction is upward trend, originally established military regime on the basis of the Continental Army can not adapt to the new international situation and the security situation in neighboring China, thereby theater system came into being. In the People’s Liberation Army is divided into five theater, theater should correspond to the east of Japan and the East China Sea direction, corresponding to the western Central Asia and India theater direction, mainly the southern theater direction corresponding to the South China Sea, the northern war zone corresponds to the direction of Russia and Mongolia, as the central theater centered coordinate strategic reserve corps.
Officers appointed theater: Theater five display a mission and future trends

Five theater and officers appointed
Officers from the theater can be seen in the appointment of some common: theater five ten military officers are “50,” so relatively young; most of them have experience working at the grassroots level, the so-called “starting in Reggie died five”, which two military officers have battlefield experience; most have received training integrated joint operations command. This shows the five main tasks entrusted to the theater and future trends:
First, combat and theater become the main task is to deter. Eastern theater commanderLiu PLA and western theater commander Zhao Zongqi are returning heroes from the battlefield, with actual combat experience, which is a valuable asset, but also the implementation of the “Military Commission to total, theater battle, armed services main building” in the implementation of the “theater of battle “organizational guarantee.
Second, the integrated joint operations will be the main model for future combat theater. The so-called “integrated joint operations” around unified combat purposes to the combat units, combat elements of highly integrated combat system as the main body, give full play to the overall combat effectiveness, in a multidimensional space combat or fight against the enemy’s fighting style. And the appointment of military officers have a theater at the National Defense University and other institutions of military education integrated joint operations experience.
Third, the theater system will be in constant development and improvement. The theater is a relatively young officers will and individual will, visionary, to accept new things, strong ability; In addition, the relatively young military officers also means working for a long time, can ensure coherence of policy implementation.
With the deepening of Chinese People’s Liberation Army to change the implementation of the system, this massive military force after the founding of foreign unbeaten mighty will rapidly improve combat effectiveness. This not only has a positive significance for peace and stability in the region and the world, but also for the new military revolution on a global scale provides a theoretical and practical aspects of the double “template.”
Original Mandarin Chinese:

习近平向五大战区授予军旗
2月1日,中国人民解放军战区成立大会在北京举行。中共中央总书记、国家主席、中央军委主席习近平向五大战区授予军旗并发布训令。组建战区联合作战指挥机构,是党中央和中央军委根据国内、国际形势变化做出的重大战略决策,将进一步推动中国部队军事改革进程,并大大提升中国人民解放军的作战能力。
改革实质:使军队编制体制适应信息化战争形态新需要
军事技术、军事力量和军队编制体制是新军事革命的三个基本要素。人类经历了漫长的冷兵器和热兵器时代之后,战争技术与军事思想在机械化战争时代迅猛发展。20世纪70年代末,苏军总参谋长、苏联元帅奥加尔科夫鉴于军事技术的飞速发展,富有前瞻性的提出了军事技术革命的设想,由此展开一场席卷全球的新军事革命;1997年,美军提出“网络中心战”概念,新军事革命的理论开始出现雏形——在每一场全面的军事革命中,均是由军事技术和武器装备的大发展推动军队编制体制变革——它是通过保证军队人员和武器装备有效结合从而使军队能够形成整体作战力量的关键。
1998年,中国提出“信息战”概念,直接指出人类第四次军事革命就是信息化的军事革命,标志着人类战争的技术形态从机械化战争时代迈向信息化战争时代。在此种背景下,中国人民解放军正是遵循着上述规律,在武器装备技术水平得到长足发展后,开始着手大力对军事体制编制进行一系列改革:2015年12月31日,军种改革机制完成,新组建了陆军、火箭军、战略支援部队三个军种,加上此前的海军和空军,形成5个军种的格局;2016年1月11日,军委机关各部门组建完成,从以前的四总部,变成了15个军委职能部门;2016年2月1日,五大战区调整完毕,以前的七大军区,调整为五大战区。
主要原因:“军区”制成为中国军事革命与军队发展的桎梏

原有七大军区制示意图
从建国初到上世纪末,受综合国力和国防投入限制,我军装备水平始终较低,未能实现完成机械化建设的目标;并且,当时国内铁路、公路建设水平较低,难以在核战争条件下支持大兵团在境内实施战略机动。受以上两点限制,我军在当时只能进行分区防御,使每个大军区都具备独立应对一个战略方向威胁的能力。
近15年以来,通过国防投入积累和军队体制改革,我国交通网络已经做到“四通八达”,我军装备水平已经得到大幅改善——初步实现机械化,部队机动作战能力大幅高,具备了从“区域防卫型”向“全域机动型”转变的基础。在机动性大大提高之后,部队在战时可能在不同区指挥下实施作战,因此就不再需要由特定的军区实施军政管理。
并且,在“军区”制度下,军区与海空军平级,又下辖军区空军,甚至是舰队,实际上是“大陆军”思想的体现,存在一定弊端:军政军令不分导致效率低下。这种体制已经成为中国军事革命与军队发展的桎梏,不能有效应对中国正在或可能面临的安全威胁。
国际格局和周边安全形势发生变化,“战区”制应时而生
战区,从地理层面来讲是一个多维空间,包括宽阔的正面、较大的纵深和可能的作战对象,它主要是根据战略战役任务而划定的战略战役军团活动区域,设有领导指挥机构,拥有对辖区部队的指挥权,是介于统帅部与战略战役军团之间的指挥层次。划分战区的主要依据包括国际格局的变化,周边安全形势,国家的军事战略,政治、经济、军事力量状况和地理环境特征等诸多方面。
改革开放以来,我国经济建设取得了举世瞩目的成就,综合国力迅速攀升带动国家战略发生变化;苏联解体后,中国陆地边境安全威胁基本消失,而来自海洋方向的安全威胁则呈上升趋势,原先建立在大陆军基础上的军区制度已经不能适应新的国际格局和中国周边安全形势,由此,战区制度应运而生。在此次解放军划分的五大战区之中,东部战区应该对应日本和东海方向,西部战区对应中亚和印度方向,南部战区则主要对应南海方向,北部战区则对应俄罗斯和蒙古方向,中部战区则作为战略预备总队居中策应。
战区主官任命:显示五大战区肩负使命与未来发展趋势

五大战区及主官任命
从此次任命的各战区主官中可以看到一些共性:五大战区的十位军政主官都是“50后”,相对年轻;大多有在基层任职经历,所谓“猛将起于卒伍”,其中有两位军事主官具有战场经历;大多接受过一体化联合作战的指挥训练。由此可见五大战区肩负的主要任务与未来发展趋势:
第一,作战和是威慑成为战区主要任务。东部战区司令员刘粤军和西部战区司令员赵宗岐都是从战场凯旋的英雄,具有实战经验,这是宝贵的财富,也是落实“军委管总、战区主战、军种主建”中落实“战区主战”的组织保证。
第二,一体化联合作战将成为未来战区的主要作战模式。所谓“一体化联合作战“,是围绕统一的作战目的,以各作战单元、作战要素高度融合的作战体系为主体,充分发挥整体作战效能,在多维作战空间打击或抗击敌方的作战样式。而此次任命的战区军事主官都有在国防大学等军事院校进修一体化联合作战的经历。
第三,战区制度还将处于不断的发展和完善中。此次战区主官都是相对年轻的上将和个别中将,思维开阔、接受新事物能力强;另外,军政主官相对年轻也意味着任职时间长,可以保证政策实施的连贯性。
随着中国人民解放军军改制度的不断深入实施,这支建国后对外大规模用兵保持全胜的威武之师将会快速提高战斗力。这不仅对于地区及世界的和平与稳定具有积极意义,也为全球范围内的新军事革命提供了理论与实践方面的双重“范本”。
Original Source: China MOD