Anxious US Military Worried about China’s Information Warfare // 焦急美國軍方擔心中國信息戰
In the past few years, the Chinese military and folk experts have set off a wave of research information warfare. After reading their works, it is not difficult to find that China’s information warfare theory research has several obvious characteristics: First, China is eager to develop its own information warfare theory, which is related to its judgment on its own security threats; secondly, China’s information War theory is deeply influenced by its traditional military command art. Both the ancient “Sun Tzu’s Art of War” and “Thirty-six”, or Mao Zedong’s people’s war thoughts have deeply imprinted in the information warfare theory; third, China’s cognition and classification of information warfare is obviously different. In the United States, the originator of information warfare, the United States, although similar to Russia’s information warfare theory, is only similar and God is not.
Wei Wei Zhao
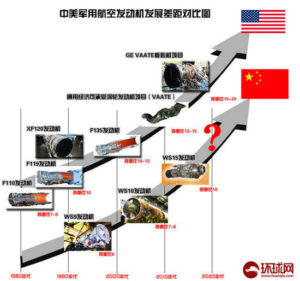
The advent of the information age has prompted people to rethink the way war is carried out. China is aware that its conventional armed forces are far less powerful than superpowers. In the near future, neither conventional forces nor nuclear weapons can pose a powerful deterrent to the United States. However, the ambitious Eastern Dragon believes that with the advent of the information age, there will be new changes in the form of war, military structure, methods of warfare and command means, and information will replace people in the future battlefield. As long as the focus of strategic research is placed on the warfare of information warfare and grasping the trend of the times, it is not difficult to shorten the distance and further gain a leading position.
In ancient China, there was a military book called “Thirty-six Meters”. One of them, “Wei Wei Zhao”, pointed out that if the enemy’s positive power is too strong, it should be avoided and it should be weak. The Chinese are used for the present, applying this strategy to the current struggle between countries – if you can’t launch a direct attack (nuclear strike), then fight information warfare, weak financial, electricity, etc.
The network system starts. Although conventional armed forces cannot compete with the United States, China’s information warfare forces theoretically threaten the political and economic security of the United States. Americans cannot afford the instant of the New York Stock Exchange and the NASDAQ stock exchange. collapse. The global accessibility of information warfare and the spread of light speed are characteristics that nuclear war does not have. What Chinese want is to defeat opponents with the speed, accuracy and continuity of information warfare.
The power of information warfare can make up for the shortcomings of conventional armed forces. The establishment of various battlefield information networks can not only improve the management level of traditional warfare, enhance the overall combat effectiveness of the troops, but also compensate for the shortage of conventional forces to a certain extent. In the eyes of the Chinese, the information warfare seems to be more powerful, and it is the force multiplier of the conventional armed forces.
Information war think tank
In 1996, Shen Weiguang, the earliest expert on information warfare in China, defined the information warfare as: “The warring parties fight for the battlefield initiative by controlling information and intelligence resources.” and the United States “protecting the friendly information system and attacking enemy information.” Compared with the definition of “system”, Shen Weiguang emphasizes “controlling” the enemy.
In 1998, the Chinese military information warfare authority Wang saves the classification of information warfare: divided into normal time, crisis time, war time according to time; divided into attack and defense according to nature; divided into country, strategy, theater, tactic according to level According to the scale, it is divided into battlefield, theater, and local war. The characteristics of information warfare include command and control warfare, intelligence warfare, electronic warfare, psychological warfare, space control warfare, hacker warfare, virtual warfare, and economic warfare. In principle, information warfare measures such as cutting off, blinding, transparent, rapid, and improving viability. General Wang’s understanding of information warfare is closer to that of the West, and he focuses on the confrontation of advanced technology.
In 1999, Chinese experts launched a big discussion on information warfare. At this time, Shen Weiguang expanded the scope of information warfare. He believes that “information warfare, broadly refers to the war against the information space and the competition for information resources in the military (including political, economic, scientific, and social fields), narrowly refers to war. The confrontation between the two parties in the field of information. It is one of the essential characteristics of modern warfare. The essence of information warfare is to achieve the ‘no war and defeat the soldiers’ by capturing the right to control the system.”
Major military expert Wang Pufeng, who is another information warfare expert in the military, has a deep understanding of information warfare. In 2000, he distinguished information warfare from information warfare. According to his explanation, information warfare refers to a form of warfare, which contains information warfare, and information warfare refers to a kind of warfare activity. He believes that “information warfare includes all combat activities, including a series of intrusion activities and computer virus attacks on enemy information and information systems, such as information theft, tampering, deletion, deception, disruption, blocking, interference, and shackles. The network is not working properly.” He advocates that China’s information warfare theory should have its own characteristics while drawing on foreign advanced combat thinking.
“Mao Network People’s War”
China’s perception of information warfare is very traditional. Many military theorists believe that the information age has given new meaning to Mao Zedong’s people’s war thoughts. Therefore, he advocates relying on and mobilizing the masses of the people to conduct online wars. It is conceivable that no matter which of the same family, playing online with 1.3 billion people is daunting.
The most important feature of the Mao Zedong-style cyber war theory is that it breaks the boundary between the military and the people. The traditional dividing line between military and civilian facilities, military technology and civil technology has been blurred. The sharing of information technology in military and civilian use has created conditions for the widespread use of civilian technology for military purposes. For example, private electronic information equipment can be used for intelligence interception and transmission. Civil communication networks can be used for war mobilization; private computers can be used for network attack and defense. Second, the difference between military and non-military personnel is gradually disappearing. With the development of network technology and the expansion of application fields, a large number of network technology talents stand out. These network elites with special abilities will become gladiators in the future network people’s war. At the same time, information networks such as communications, transportation, and financial systems and international networking have provided the necessary conditions for China to carry out the people’s war.
Today, the idea of the people’s war has been established as the fundamental guiding principle of China’s network information warfare. A Chinese military author wrote: “The strategic and tactical principles of flexible maneuvering are still the soul of network information warfare. The broad masses of the people actively participate in the war, especially the technical support and online warfare, which is the mass base and strength to win the victory of the network information war. Source.”
The power of the Internet People’s War is so terrible. Perhaps we can understand why the Chinese are willing to reduce the size of their armed forces. Imagine that once the war breaks out, China can launch a large number of people to participate in the war, information engineers and civilians will be organized through the home. When computers attack the US network information system, why should we maintain a large-scale combat force?
Information war drill
In the past few years, China has conducted several major information warfare military exercises to test the information warfare theory. The first “special warfare” (information warfare) drill was conducted in October 1997. A group army in a military region was attacked by a virus designed to smash its system. The group used military anti-virus software to defend it. The drill was called “invasion and anti-invasion drills.” Ground logistics, medical and air force units were also used during the exercise.
In October 1998, China held a high-tech comprehensive exercise jointly conducted by the three major military regions. For the first time in the joint defense operations exercise, the “military information highway” was used. The information network system in the command automation system consists of digital, dialing, command network and secret channel. The other parts of the command automation system are subsystems for command operations, audio and graphics processing, control, and data encryption.
In October 1999, the PLA conducted the first battle-level computer online confrontation exercise between two group armies. Reconnaissance and anti-reconnaissance, interference and anti-interference, blockade and anti-blockade, air strikes and anti-air strikes. In the software environment, six types of operations such as resource sharing, operational command, situation display, auxiliary evaluation, signal transmission and intelligence warfare were carried out. The computer evaluation system performs data and quality analysis on the performance of both sides of the exercise.
In July 2000, a military region also conducted an online confrontation drill. The three training tasks related to this exercise are: organizing and planning campaigns, seizing air and information rights, implementing breakthroughs and counter-breakthroughs. More than 100 terminals were connected to the walkthrough.
Militia detachment
China’s people’s war has a complete system. Its overall development direction is “the combination of a capable standing army and a strong reserve force.” This national defense system is conducive to giving full play to the overall effectiveness of the people’s war and the advantages of “network tactics.”
China’s 1.5 million reserve forces are very keen on playing the online people’s war. In some areas, the PLA has compiled reserve forces into small information warfare units. For example, in Yichang City, Hubei Province, the military division organized 20 municipal departments (electricity, finance, television, medical, etc.) technical personnel to set up a reserve information warfare. The department has a network battle camp, an electronic war camp, an intelligence psychological war camp and 35 technical teams. The Ministry also established the first reserve information warfare training base in China that can accommodate 500 people.
Yichang is not the only area where the reserve and militia are trained in information warfare. In December 1999, a reserve and militia meeting was held in Xiamen, Fujian. In the subsequent exercises, the militia detachment with high-tech equipment carried out electronic countermeasures, cyber attacks and protection, and radar reconnaissance performances. The goal of the imaginary attack is an island that is surrounded, so it is easy for outsiders to think of Taiwan. Xiamen is a special economic zone that brings together a large number of high-tech talents, so it has the superior conditions for implementing information warfare.
In an exercise held by the Jinan Military Region, the Xi’an People’s Armed Forces Information Warfare Division played the blue party responsible for the attack. They developed 10 information warfare measures, including information mines, information reconnaissance, alteration of network information, release of information bombs, and dumping. Web spam, distribution of network flyers, information spoofing, dissemination of false information, organization of information defense, establishment of cyber espionage stations. It can be seen from these network information warfare methods that their research on network information warfare has been quite specific and in-depth.
Chinese military experts also suggest that militia organizations at all levels should set up network technology professional detachments. In order to facilitate command and coordination, the militia network technology professional detachment should implement grouping and vertical management in the province or region. The reserve forces participate in the “network attack and defense” and “network technology guarantee” in the future war, and their actions must be implemented and unified by the military organization.
Medium
The Chinese People’s Liberation Army has developed its own set of information warfare education methods. The steps are: first, teach the basic knowledge of network information warfare; secondly, improve the information warfare knowledge level by telling the advanced military thoughts of foreign troops; then improve the information warfare use skills, especially Electronic technology, psychological warfare techniques, and information offensive and defensive techniques; finally, through exercises, knowledge is translated into practical operational capabilities. In China, it is mainly the responsibility of the PLA Academy to train high-tech talents in information warfare:
The People’s Liberation Army Communication Command College is located in Wuhan. In 1998, the Institute published two books, Information Command and Control Science and Information Warfare Technology. These two books are the most important textbooks for information warfare education in China. The college enjoys a high reputation for its excellent information warfare tutorials, which analyze information warfare requirements at the strategic, operational, and tactical levels.
The People’s Liberation Army Information Engineering University, located in Zhengzhou, was formed by the merger of the former People’s Liberation Army Information Engineering College, Electronic Technology College and Surveying and Mapping College. The school’s current main research areas are information security, modern communication technology and space technology, and exploration in some cutting-edge disciplines, such as remote sensing information technology, satellite navigation and positioning technology, geographic information database technology.
The PLA University of Science and Technology, located in Nanjing, was formed by the merger of the former People’s Liberation Army Communication Engineering College, the Engineering Corps Engineering College, the Air Force Meteorological College and the General Staff No. 63 Research Institute. The school specializes in training military personnel in information warfare, command automation and other new disciplines. Nearly 400 experts and professors are engaged in information warfare theory and technology research at the university.
The National Defense Science and Technology University of the People’s Liberation Army is located in Changsha. The school is directly affiliated to the Central Military Commission. Has developed the famous “Galaxy” series supercomputer. During the Kosovo War between April and June 1999, nearly 60 senior officers gathered here to study high-tech wars.
The Naval Engineering University of the People’s Liberation Army, located in Wuhan, is the only institution in the Navy that studies information warfare. The purpose of the school’s research information warfare is to apply information technology to naval equipment so that the Chinese navy can adapt to information warfare.
in conclusion
What conclusions can we draw from China’s information warfare research? What lessons can the US military get from it?
First, Chinese military theorists have found a cheap and effective method of information warfare that gives China a position equal to that of the West in terms of strategic military and international status, thus enabling China to play a more important strategic role in the Asian region.
Second, China’s emphasis on new information warfare forces is extraordinary. Therefore, it is possible to develop various forms of information warfare forces, such as: network forces (independent units), “network warriors” raid units, information protection units, information units, electronic police and joint network people’s war organizations. Interestingly, in terms of current capabilities, Western countries, not China, have the ability to put these ideas into practice.
Third, China’s information warfare theory reflects the combination of Western and Chinese thoughts, and the influence of the former is getting weaker. Due to some common sources of military command art (Marxist dialectical thinking), China’s information warfare is more similar to Russia. However, by its very nature, China’s information warfare theory is different from Russia and the West. China’s information warfare theory emphasizes control, computerized warfare, cyber warfare, knowledge warfare, and information rights.
Fourth, in the field of information warfare, China has crossed several stages of technological development, and using the technology of the Quartet has not only saved time but also saved money. However, China does not fully emulate foreign countries, but adopts a creative information warfare strategy. But no matter what, China is a different information warfare force that is worthy of attention.
For the US military, studying China’s information warfare theory is not just to provide the military with several opinions. “Sun Tzu’s Art of War” said that “knowing that he knows, has won every battle.” From the perspective of foreign information warfare theory to analyze the information warfare capabilities of the United States, we can discover the fatal flaws of the US information warfare system.
As the Chinese say, the losers of information warfare are not necessarily technically backward, and those who lack the ability to direct art and strategy are most likely to be losers. It is time for the United States to reflect on its own information warfare and to study information warfare strategies and tactics.
Original Mandarin Chinese:
在過去幾年裡,中國軍方與民間專家們掀起了研究信息戰的熱潮。閱讀他們的作品後不難發現,中國的信息戰理論研究具有幾個明顯的特徵:首先,中國正迫不及待地發展自己的信息戰理論,這與其對自身安全威脅的判斷有關;其次,中國的信息戰理論受其傳統軍事指揮藝術影響頗深。無論是古代的《孫子兵法》和《三十六計》,還是毛澤東的人民戰爭思想都在信息戰理論中打下了深深的烙印;第三,中國對信息戰的認知與分類,顯然不同於信息戰的開山鼻祖——美國,雖近似於俄國的信息戰理論,卻也只是形似而神不是。
圍魏救趙
信息時代的到來促使人們對戰爭的進行方式重新進行思索。中國意識到其常規武裝力量與超級大國相比實力懸殊,近期內無論是常規力量還是核武器,中國都無法對美國構成強大威懾。但是,雄心勃勃的東方巨龍認為:隨著信息時代的來臨,戰爭形態、軍隊結構、作戰方式和指揮手段都會有嶄新的變化,信息將取代人充斥於未來戰場。只要把戰略研究的著眼點放到信息戰這一戰爭形態上,把握時代發展潮流,就不難縮短距離,並進一步取得領先地位。
中國古代有部兵書叫《三十六計》,其中的一計“圍魏救趙”就指出,如果敵人正面力量過於強大,應當避實就虛,擊其薄弱之處。中國人古為今用,把這個計謀應用到當前國家間鬥爭——如果你不能發動直接攻擊(核打擊),那就打信息戰,向西方薄弱的金融、電力等
網絡系統下手。常規武裝力量雖然無法與美國抗衡,然而,中國的信息戰部隊在理論上卻實實在在威脅到美國的政治及經濟安全,美國人無法承受紐約股票交易所和納斯達克股票交易所在瞬間崩潰。信息戰的全球可及性、光速傳播性是核戰爭所不具有的特性,中國人要的就是以信息戰的速度、準確性和持續性擊敗對手。
信息戰力量可彌補常規武裝力量的不足。各種戰場信息網絡的建立,不僅可以提高對傳統戰爭的管理水平,增強部隊的整體戰鬥力,還可以在一定程度上彌補常規力量的不足。在中國人眼中,信息戰好似如虎添翼,是常規武裝部隊的力量倍增器。
信息戰智囊
1996年,中國最早提出信息戰的專家沈偉光給信息戰下的定義是:“交戰雙方通過控制信息與情報資源來爭奪戰場主動權的戰爭。”與美國“保護友方信息系統,攻擊敵方信息系統”的定義相比,沈偉光更強調“控制”敵人。
1998年,中國軍方信息戰權威王保存少將對信息戰進行了分類:按時間分為平時、危機時、戰時;按性質分為進攻、防禦;按層次分為國家、戰略、戰區、戰術;按規模分為戰場、戰區、局部戰爭。信息戰表現的特徵包括指揮與控制戰、情報戰、電子戰、心理戰、空間控制戰、黑客戰、虛擬戰、經濟戰等方面的較量。信息戰原則上採取切斷、蒙蔽、透明、快速和提高生存力等措施。王將軍對信息戰的認識與西方較為接近,都把重點放在先進技術的對抗上。
1999年,中國專家對信息戰展開了大討論。沈偉光此時把信息戰的範圍擴大,他認為“信息戰,廣義地指對壘的軍事(也包括政治、經濟、科技及社會一切領域)集團搶占信息空間和爭奪信息資源的戰爭,狹義地指戰爭中交戰雙方在信息領域的對抗。它是現代戰爭的本質特徵之一。信息戰的本質在於通過奪取制信息權達到’不戰而屈人之兵’。”
軍方另一位信息戰專家王普豐少將對信息戰有很深入的理解,2000年,他把信息戰和信息戰爭區別開。根據他的解釋,信息戰爭指的是一種戰爭形態,它包含了信息戰,而信息戰指的是一種作戰活動。他認為“信息戰包括所有作戰活動,其中有對敵信息及信息系統實施信息竊取、篡改、刪除、欺騙、擾亂、阻塞、干擾、癱瘓等一系列的入侵活動和計算機病毒攻擊,最終使敵計算機網絡無法正常工作。”他主張中國的信息戰理論在藉鑒國外先進作戰思想的同時,應具有中國自己的特色。
“毛式網絡人民戰爭”
中國對信息戰的認知非常具有傳統特色。許多軍事理論家認為信息時代賦予了毛澤東人民戰爭思想新的內涵,因此,主張依靠和發動廣大人民群眾進行網上戰爭。可以想像,無論是哪個同家,與13億人打網絡戰都是令人生畏的。
毛澤東式網絡人民戰爭理論的最重要特徵是它打破了軍與民的界限。模糊了軍用設施與民用設施、軍用技術與民用技術的傳統分界線。信息技術在軍用和民用上的共享,為廣泛利用民間技術達成軍事目的創造了條件。例如,可以利用民間的電子信息設備進行情報截獲和傳輸可以利用民間的通信網絡進行戰爭動員;可以利用民間的計算機進行網絡進攻和防禦等。其次,軍事人員與非軍事人員的區別也在逐漸消失。隨著網絡技術的發展和應用領域的擴大,大批的網絡技術人才脫穎而出。這些具備特殊能力的網絡精英將成為未來網絡人民戰爭中的角斗士。與此同時,通信、交通、金融系統等信息網絡與國際聯網,為中國開展人民戰爭提供了必要條件。
如今,人民戰爭思想已經被確立為中國網絡信息戰的根本指導原則。一個中國軍方作者寫道:“靈活機動的戰略戰術原則,仍然是網絡信息戰的靈魂。廣大人民群眾積極參戰,特別是技術支援和網上參戰,則是奪取網絡信息戰勝利的群眾基礎和力量源泉。”
網絡人民戰爭的威力是如此可怕,或許,我們可以明白為何中國人願意削減其武裝部隊規模了——設想一旦戰爭爆發,中國可以發動大量民眾參戰,信息工程師和平民將被組織起來,通過家中的電腦攻擊美國的網絡信息系統,那又何必要維持規模龐大的作戰部隊呢?
信息戰演練
過去幾年裡,中國舉行過數次重大信息戰軍事演習對信息戰理論進行檢驗。首次“特種戰”(信息戰)演練於1997年10月進行。某軍區的一個集團軍遭到旨在癱瘓其係統的病毒攻擊,該集團軍用殺毒軟件進行了防衛。該演練被稱為“入侵與反入侵演練”。演習時還動用了地面後勤、醫療和空軍部隊。
1998年10月,中國舉行了一場由三大軍區聯合進行的高科技綜合演練。聯合防禦作戰演練中首次使用了“軍事信息高速公路”。指揮自動化系統中的信息網絡系統由數字、撥號、指揮網和保密信道組成。指揮自動化系統的其他部分是指揮作戰、音頻和圖形處理、控制和數據加密等子系統。
1999年10月,解放軍首次進行了兩個集團軍之間的戰役級計算機網上對抗演習。演練了偵察與反偵察、干擾與反干擾、封鎖與反封鎖、空襲與反空襲等科目。在軟件環境下進行了資源共享、作戰指揮、態勢顯示、輔助評估、信號傳輸和情報戰等6類作業。計算機評估系統對演習雙方的表現進行數據與質量分析。
2000年7月,某軍區也進行了網上對抗演練。與此次演練有關的3項訓練任務是:組織和計劃戰役、奪取制空權和製信息權、實施突破和反突破。有100多台終端聯網參與了演練。
民兵分隊
中國的人民戰爭有一套完備的體制,其總體發展方向是“精幹的常備軍與強大的後備力量相結合”,這種國防體制有利於發揮人民戰爭的整體效能和“網海戰術”優勢。
中國150萬預備役部隊十分熱衷於打網絡人民戰爭。在一些地區,解放軍已經把預備役部隊編成小型信息戰部隊。例如,在湖北省宜昌市,軍分區組織了20個市政部門(電力、財政、電視、醫療等)的技術人員成立了預備役信息戰團。該部擁有網絡戰營、電子戰營、情報心理戰營及35個技術分隊。該部還建立了中國第一個能容納500人的預備役信息戰訓練基地。
宜昌並不是組織預備役和民兵進行信息戰訓練的唯一地區。 1999年12月在福建廈門召開了預備役和民兵會議。在隨後進行的演習中,擁有高技術裝備的民兵分隊進行了電子對抗、網絡攻擊和防護、雷達偵察表演。山於假想攻擊的目標是一座被包圍的島嶼,因此很容易讓外人聯想到是針對台灣。廈門是經濟特區,匯集了大量高科技人才,因此有實施信息戰的優越條件。
在一次由濟南軍區舉行的演習中,西安人武部信息戰分隊扮演負責攻擊的藍方,他們制定了10種信息戰措施,其中有安放信息地雷、信息偵察、改動網絡資料、釋放信息炸彈、傾倒網絡垃圾、分發網絡傳單、信息欺騙、散佈虛假信息、組織信息防禦、建立網絡間諜站。從這些網絡信息戰法可以看出,他們對網絡信息戰的研究已相當具體、深入。
中國的軍事專家還建議,各級民兵組織都應成立網絡技術專業分隊,為便於指揮協調,民兵網絡技術專業分隊應以省或者地區為單位實行條條編組,垂直管理。後備力量參與未來戰爭中的“網絡攻防”和“網絡技術保障”,其行動要由軍隊組織實施和統一協調。
培養基地
中國人民解放軍發展出自己的一套信息戰教育方法,其步驟是:首先傳授網絡信息戰基礎知識;其次通過講述外軍的先進軍事思想提高信息戰知識水平;然後提高信息戰使用技能,特別是電子技術、心理戰技術和信息攻防技術;最後,通過演習把知識轉化為實際操作能力。在中國,主要由解放軍院校擔負培養信息戰高技術人才的責任:
解放軍通信指揮學院,位於武漢。 1998年,該院出版了兩部書籍,分別是《信息作戰指揮控制學》和《信息作戰技術學》,這兩部書籍是中國信息戰教育最重要的教材。該學院以其優良的信息戰教程設置而享有很高的聲譽,這些教程分析了戰略、戰役、戰術層次的信息作戰要求。
解放軍信息工程大學,位於鄭州,由原解放軍信息工程學院、電子技術學院和測繪學院合併而成。該校目前主要研究領域是信息安全,現代通信技術和空間技術,並且在一些尖端學科領域進行探索,如遙感信息技術、衛星導航與定位技術、地理信息數據庫技術。
解放軍理工大學,位於南京,由原解放軍通信工程學院、工程兵工程學院、空軍氣象學院和總參第63研究所合併而成。該校專門負責訓練信息戰、指揮自動化和其它新學科的軍事人才。有近400名專家教授在該大學從事信息戰理論與技術研究。
解放軍國防科技大學,位於長沙,該校直接隸屬於中央軍委。曾開發了著名的“銀河”系列超級計算機。 1999年4月到6月科索沃戰爭期間,近60名高級軍官匯集在此研究高科技戰爭。
解放軍海軍工程大學,位於武漢,是海軍唯一研究信息戰的院校。該校研究信息戰的目的是把信息技術應用到海軍裝備,使中國海軍能適應信息化戰爭。
結論
我們從中國的信息戰研究中能得到什麼結論呢?美國軍隊又能從中得到什麼啟示呢?
首先,中國的軍事理論家找到了一廉價而有效的信息戰方法,它使中國在戰略軍事和國際地位上取得與西方相等的位置,從而使中國在亞人地區發揮更重要的戰略角色。
其次,中國對新型信息戰部隊的重視非同尋常。因此可能會發展形式各樣的信息戰部隊,例如:網絡部隊(獨立兵種)、“網絡勇士”突襲分隊、信息保護部隊、信息兵團,電子警察和聯合網絡人民戰爭機構。有意思的是,就現階段的能力而言,西方國家,而不是中國,更具有把這些設想付諸實施的能力。
第三,中國的信息戰理論反映了西方和中國思想的結合,而且前者的影響力越來越弱。由於軍事指揮藝術的一些共同淵源(馬克思主義辯證思想),中國的信息戰思想更類似於俄國。但是,就其本質而言,中國的信息戰理論與俄國和西方都不同。中國的信息戰理論強調控制、電腦化戰爭、網絡戰、知識戰和製信息權。
第四,在信息戰領域,中國跨越了若干技術發展階段,利用四方的技術,不僅節省了時間而且還節省了金錢。不過,中國沒有完全仿效外國,而是採用創造性的信息戰策略。但不管怎麼樣,中國都是值得關注的一支不同於其他國家的信息戰力量。
對美軍而言,研究中國的信息戰理論絕非僅僅為了給軍方提供幾條意見。 《孫子兵法》稱“知彼知已,百戰百勝”。從外國信息戰理論的角度來分析美國的信息戰能力,才能發現美國信息戰系統的致命缺陷。
正如中國人所言,信息戰的失敗者不一定是技術落後方,那些缺乏指揮藝術和戰略能力的人才最可能是失敗者。美國到了該反省自己的信息戰思想,並研究信息戰戰略和戰術的時候了。
Original Referring url: